Automate VLAN configuration and keep your switches perfectly in sync.
Imagine setting up a large office network with switches on every floor. Each department—HR, Sales, IT—needs its own VLAN to keep traffic separated and organized. Creating the same VLANs manually on every switch is time-consuming and error-prone. A typo in a VLAN name or number, or a forgotten switch, could cause problems.
Cisco created the VLAN Trunking Protocol (VTP) to solve this.
VTP operates at Layer 2 of the OSI model (the Data Link Layer) and automatically shares VLAN information among all switches in the same VTP domain. When you create, delete, or rename a VLAN on one switch, VTP sends that update to all other switches—keeping every device synchronized without manual configuration.
By the end of this lesson, you will be able to:
- Discover what VTP does and why it helps manage VLANs easily.
- Set up a VTP domain name so switches can share VLAN information.
- Learn the three VTP modes:
Server, Client, and Transparent— and what each one does. - Practice using Cisco CLI commands (in Packet tracer) to see how switches share and update VLANs in a network.
Understanding VTP
Imagine a large office building with multiple network switches — one on each floor.
Each floor has different departments (Finance, HR, Engineering), and each department should have its own VLAN for isolation and security.
If you had to manually create VLANs on each switch for every department, you’d be repeating the same configuration over and over again. This increases the chance of typos, inconsistencies, and wasted time.
VTP solves this by acting as an “information distributor.”
- One switch acts as the VTP Server — it creates and manages the VLAN list.
- Other switches can act as Clients, automatically receiving updates about VLANs from the server.
- A Transparent switch ignores these updates but can still forward them to other switches.
Think of VTP as a company newsletter system:
- The server writes and publishes the newsletter (VLAN updates).
- The clients receive and read it (replicating VLANs).
- The transparent switches simply pass the newsletter along without editing or reading it.
VTP Operation Modes
| Mode | Description | Can Create/Delete VLANs? | Propagates VLANs? | Receives VLAN Updates? |
|---|---|---|---|---|
| Server | Default mode. Manages VLAN database and advertises VLAN information to the domain. | ✅ Yes | ✅ Yes | ✅ Yes |
| Client | Cannot create, delete, or rename VLANs. Relies entirely on updates from servers. | ❌ No | ❌ No | ✅ Yes |
| Transparent | Operates independently. Forwards VTP messages but does not synchronize VLANs. | ✅ Yes (local only) | ❌ No | ❌ (does not update its own VLANs) |
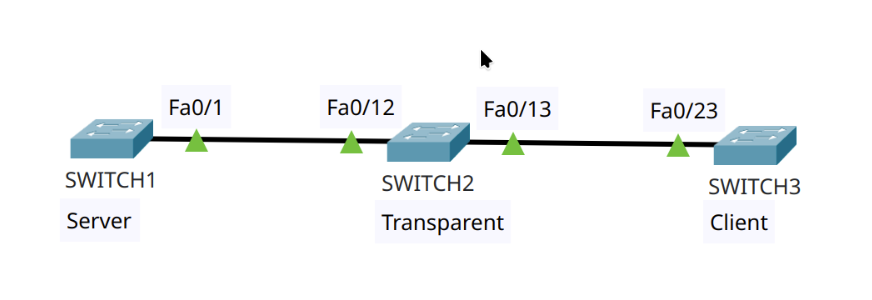
Lab Topology Overview
In this lab, you’ll need three switches connected with trunk links. Use the hostname command to rename each device before starting the configuration.
- Switch1 — VTP Server
- Switch2 — VTP Transparent
- Switch3 — VTP Client
These switches are all part of the same VTP domain: ccnalab
Command Summary
| Command | Description |
|---|---|
enable | Enter privileged EXEC mode |
configure terminal | Enter global configuration mode |
show running-config | Display current configuration |
show vlan brief | Display VLAN list, names, and ports |
show vtp status | Display VTP configuration and mode |
vtp domain <domain-name> | Set the VTP domain name |
| vtp version {1 | 2 | 3} | Set the VTP version (in Packet Tracer ver. 1 & 2 are available) |
| vtp mode {server | transparent | cliente} | Set the VTP mode |
vlan <number> [name <vlan-name>] | Create or name a VLAN |
Step-by-Step Lab
Task 1: Configure the VTP Domain
Goal: Set up a VTP domain called ccnalab on Switch1 and ensure all switches belong to this domain.
Step 1: Check Current VTP Status
Switch1> enable
Switch1# show vtp statusExpected output:
VTP Operating Mode : Server
VTP Domain Name :By default, the domain name is NULL, meaning no domain has been configured.
Repeat the same command on Switch2 and Switch3.
They will also show VTP Domain Name: NULL.
Step 2: Set the Domain Name on Switch1
Switch1# configure terminal
Switch1(config)# vtp domain ccnalab
Output:
Changing VTP domain from NULL to ccnalab
Important Notes:
- The VTP domain name is case-sensitive —
ccnalab, ccnaLab, and CCNALABare different. - Once set, a domain name cannot be erased (only replaced).
- All switches in the same domain must use identical names.
Step 3: Verify VTP Domain Synchronization
After setting vtp domain ccnalab on Switch1, check all switches again:
Switch2# show vtp status
Switch3# show vtp statusOutput:
VTP Domain Name : ccnalab
Even though you only configured Switch1, the other switches automatically joined the same domain because they received VTP advertisements from Switch1.
Task 2: Configure VTP Modes
Goal: Assign each switch its correct mode — Server, Transparent, or Client.
Step 1: Confirm Current Mode
Switch1# show vtp statusOutput:
VTP Operating Mode : ServerAll switches default to Server mode initially.
Step 2: Configure Switch2 as Transparent
Switch2# configure terminal
Switch2(config)# vtp mode transparentOutput:
Setting device to VTP TRANSPARENT mode.Verification:
Switch2# show vtp status
VTP Operating Mode : TransparentBehavior: Transparent mode switches do not participate in VTP synchronization. They forward advertisements but do not apply them.
Step 3: Configure Switch3 as Client
Switch3# configure terminal
Switch3(config)# vtp mode clientOutput:
Setting device to VTP CLIENT mode.Verification:
Switch3# show vtp status
VTP Operating Mode : ClientBehavior: Client mode switches cannot create or delete VLANs. They depend entirely on updates from a VTP server.
Task 3: Verify VTP Operation
Goal: Test how VLAN creation behaves across different modes.
Step 1: Display Existing VLANs
Switch1# show vlan brief
Switch2# show vlan brief
Switch3# show vlan briefDefault VLANs: 1, 1002, 1003, 1004, 1005
Step 2: Create VLAN 10 on Switch1 (Server)
Switch1# configure terminal
Switch1(config)# vlan 10
Switch1(config-vlan)# name SALES
Switch1(config-vlan)# exitVerify:
Switch1# show vlan briefVLAN 10 appears as active.
Because Switch1 is a VTP server, the new VLAN automatically propagates to Switch3 (Client) but not to Switch2 (Transparent).
Check:
Switch2# show vlan brief → VLAN 10 missing
Switch3# show vlan brief → VLAN 10 presentResult: VLAN 10 replicated only to Switch3.
Step 3: Create VLAN 20 on Switch2 (Transparent)
Switch2# configure terminal
Switch2(config)# vlan 20
Switch1(config-vlan)# name HR
Switch1(config-vlan)# exitVerification:
Switch2# show vlan brieVLAN 20 appears locally, but does not propagate to Switch1 or Switch3.
Result: VLAN 20 is local-only to Switch2.
Step 4: Create VLAN 30 on Switch3 (Client)
Switch3(config)# vlan 30Error:
VTP VLAN configuration not allowed when device is in CLIENT mode.You cannot create VLANs in client mode.
Step 5: Create VLAN 30 on Switch1 (Server)
Switch1# configure terminal
Switch1(config)# vlan 30
Switch1(config-vlan)# name IT
Switch1(config-vlan)# exitVerification:
Switch1# show vlan brief
Switch3# show vlan briefVLAN 30 appears on both Switch1 and Switch3.
Switch2 forwards the VTP advertisement but does not apply it.
Final VLAN list:
- Switch1 (Server): VLANs 1, 10, 30
- Switch2 (Transparent): VLANs 1, 20
- Switch3 (Client): VLANs 1, 10, 30
How VTP Synchronization Works: Conceptual Analogy
Picture three coworkers sharing files:
- The Server keeps the master folder and updates everyone.
- The Client automatically syncs its files from the server.
- The Transparent coworker doesn’t join the shared folder but passes updates along to others.
Whenever you create a new VLAN on a server, VTP packages that information into advertisements and sends it over trunk links to all connected switches in the same domain.
These VTP advertisements contain:
- VTP version (1, 2, or 3)
- Domain name
- Configuration revision number
- List of VLANs
The configuration revision number increases whenever the VLAN database changes.
Clients use this number to determine if the update is newer and should replace their VLAN list.
Common Troubleshooting Cisco CLI Commands
| Command | Purpose | Typical Use Case |
|---|---|---|
show vtp status | Displays current VTP mode, domain, version, and revision number | Verify domain consistency and mode |
show vlan brief | Lists all active VLANs | Check whether VLANs have propagated correctly |
show interfaces trunk | Displays trunk link status | Confirm that trunking is active between switches |
vtp mode ? | Shows available VTP modes | Check supported configurations |
vtp domain <name> | Defines VTP domain | Ensure all switches share the same domain |
vtp password <string> | (Optional) Adds VTP authentication | Prevents unauthorized VLAN updates |
Key Takeaways
- VTP automates VLAN distribution, reducing administrative workload.
- All switches in a domain must share the same domain name and trunk links.
- Server Mode: Can create, delete, and propagate VLANs.
- Client Mode: Receives and applies VLANs but cannot modify them.
- Transparent Mode: Creates local VLANs and forwards advertisements but ignores them.
- VTP domain names are case-sensitive and cannot be removed once set.
- VLANs only propagate over trunk links.
Quick Reference: VTP Troubleshooting Commands
# Display VTP status
Switch# show vtp status
# Display VLANs
Switch# show vlan brief
# Verify trunk links
Switch# show interfaces trunk
# Configure VTP domain
Switch(config)# vtp domain [domain]
# Change VTP mode
Switch(config)# vtp mode {server | client | transparent}
# Create VLAN
Switch(config)# vlan 10
Switch(config-vlan)# name [NAME]
Summary
VTP is a powerful Cisco feature that keeps VLAN configurations consistent across the network. When implemented properly, it can save hours of manual configuration. However, it must be handled carefully: one misconfigured switch with a higher revision number can overwrite VLAN databases across the domain.
Always remember to:
- Verify VTP domain name and mode before adding a new switch.
- Use
show vtp statusfrequently. - Keep backups of VLAN databases before large-scale updates.
By understanding and mastering VTP, you gain a deeper control of Layer 2 network automation and scalability — a fundamental skill for every Cisco-certified network engineer.
Questions, comments, or just wanna drop a “hey”?
Go ahead — Just shoot an email to: fromzerotoccna@gmail.com
