IPsec Remote Access
IPsec Remote Access allows users outside the office to connect securely to internal company resources. It creates an encrypted path between the remote user and the corporate network, ensuring privacy, authenticity, and protected communication. It’s important to note that IPsec itself is not the VPN, but rather the security framework that protects the VPN connection. The goal is simple: allow remote access without exposing the internal network to the internet.
Overview
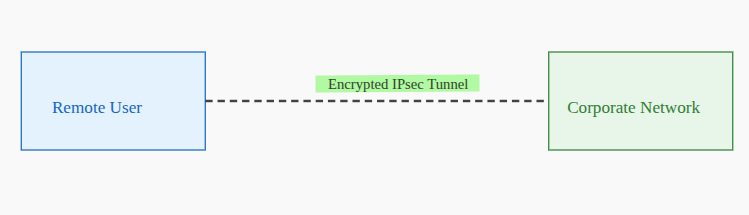
The diagram shows a remote user on the left and the corporate network on the right. Between them, there is a Encrypted IPsec Tunnel.
The (dashed) line represents the secure encrypted connection created by IPsec. It indicates that all communication between the remote user and the company’s internal network travels through this protected tunnel, preventing unauthorized access or interception. In short, the diagram visually explains how a remote user connects safely to the corporate network using an IPsec-based VPN tunnel.
Explanation:
A remote user connects to the corporate network through an encrypted tunnel. All traffic between both ends is protected by IPsec, preventing interception or manipulation.
Key Concepts
Tunnel Mode
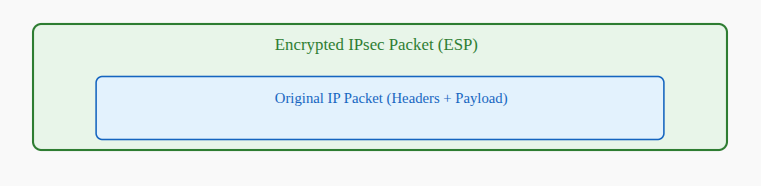
IPsec wraps the entire original packet in a new encrypted packet. This fully protects the communication.
IKEv1/IKEv2
These protocols negotiate how the tunnel will be built.
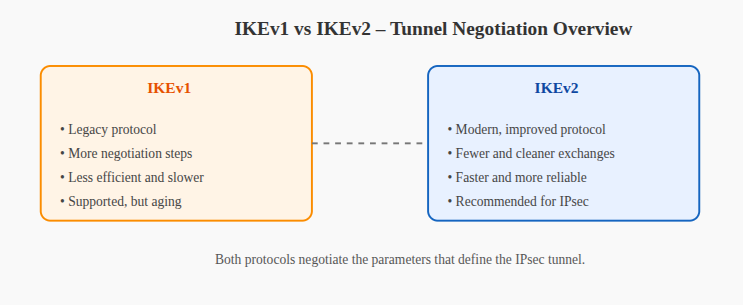
- IKEv1 = older, more steps
- IKEv2 = faster, cleaner, recommended
ESP (Encapsulating Security Payload)
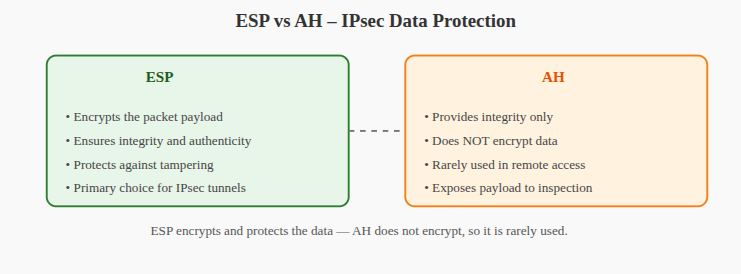
ESP encrypts the data and ensures no one tampers with it.
This is why AH is rarely used — AH does not encrypt.
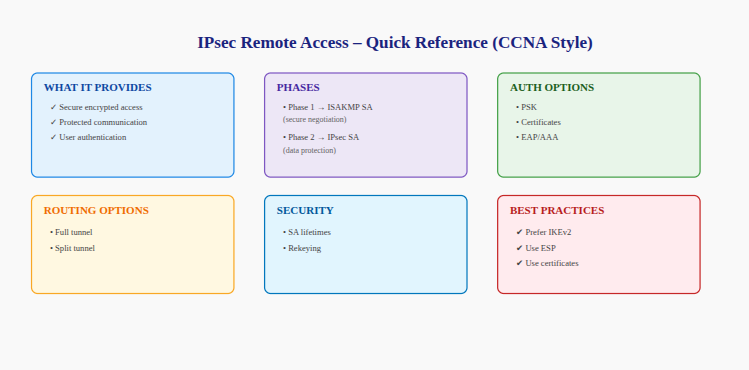
Authentication Methods
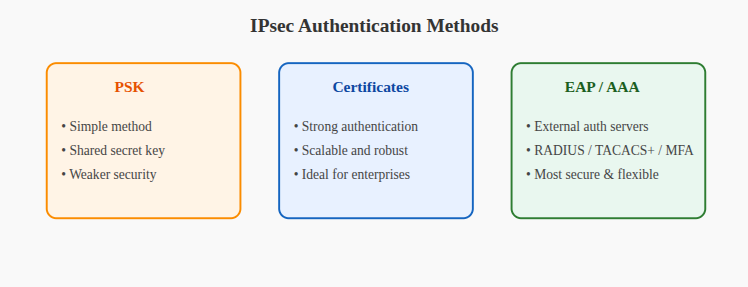
- PSK: simple, but weaker
- Certificates: stronger, scalable
- EAP/AAA: integrates external authentication servers (RADIUS/TACACS+/MFA)
Split Tunneling

Controls whether all traffic goes through the VPN or only internal traffic.
Operational Flow
(Client) ---> [IKE Phase 1] ---> [IKE Phase 2] ---> [Tunnel Active]Step-by-step explanation:
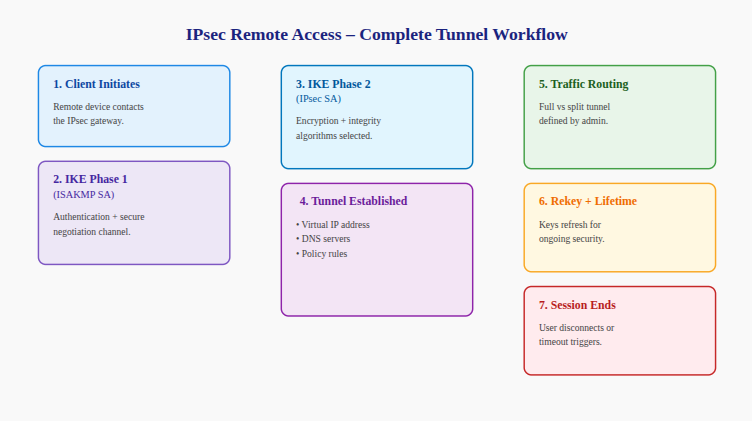
- Client Initiates
The remote device attempts to connect to the IPsec gateway. - IKE Phase 1 (ISAKMP SA)
Both sides authenticate and agree how to protect further negotiation. - IKE Phase 2 (IPsec SA)
They decide which encryption and integrity algorithms will protect the actual data. - Tunnel is Established
The user receives:- a virtual IP address
- DNS servers
- policy rules
- Traffic Routing
The admin decides between full tunnel or split tunnel. - Rekeying / Lifetime Control
Keys refresh periodically for security. - Session Ends
Either manually or by timeout.
The Maps
Full Tunnel

The user’s entire connection flows through the company.
Split Tunnel

Only business traffic uses the VPN.
Security Association Map
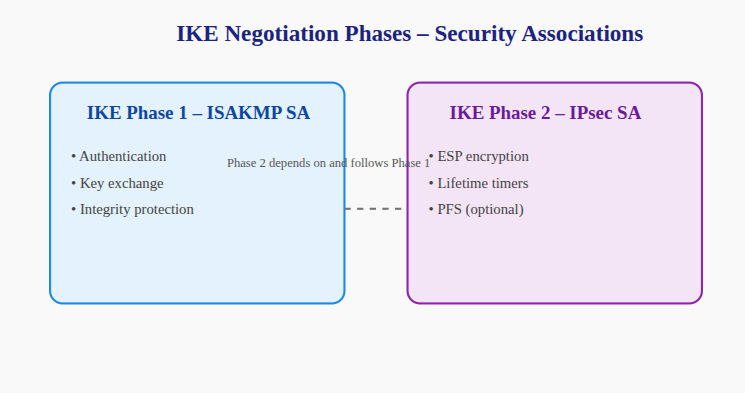
Each SA is like a rulebook that defines how traffic must be protected.
Components Table
| Component | Purpose | Explanation |
|---|---|---|
| IKE Phase 1 | ISAKMP SA | Builds the secure negotiation channel |
| IKE Phase 2 | IPsec SA | Defines encryption for user data |
| Authentication | Identity validation | PSK, certificates, or AAA |
| ESP | Encryption + integrity | Main protocol for secure data |
| Client | End-user platform | Windows/macOS/Linux/mobile |
| Access Control | Resource permission | ACLs + policies |
Concept Schema

Cisco CLI
crypto isakmp policy 10
encryption aes 256
hash sha256
authentication pre-share
group 14
crypto ipsec transform-set RA-SET esp-aes 256 esp-sha-hmac
ip local pool RA-POOL 10.10.100.1 10.10.100.50
crypto map RA-MAP 10 ipsec-isakmp
set peer x.x.x.x
set transform-set RA-SET
match address RA-ACL
IPsec Remote Access Quick Guide
CCNA Practice Quiz
Q1. What role do security associations play?
Q2. Why is ESP preferred over AH?
Q3. How does IKEv2 improve tunnel setup compared to IKEv1?
Q4. What distinguishes full tunneling from split tunneling?
Q5. What authentication mechanisms can be used?
Answers
A1. They define how the tunnel is secured: encryption, hashing, lifetimes, and keys.
A2. ESP encrypts the data and provides integrity. AH only verifies integrity — it does not encrypt.
A3. It is faster, simpler, requires fewer exchanges, and handles mobility more reliably.
A4. Full tunnel sends all traffic through VPN; split tunnel sends only internal traffic through VPN.
A5. PSK, certificates, and EAP/AAA (RADIUS, TACACS+, MFA).
Questions, comments, or just wanna drop a “hey”?
Go ahead — Just shoot an email to: fromzerotoccna@gmail.com
