SSH or Secure Shell
SSH (Secure Shell) is a protocol that lets you safely access and control remote devices over a network. It encrypts all traffic so passwords and commands can’t be intercepted. Engineers use SSH to manage routers, switches, servers, and Linux systems without exposing sensitive data. It replaces older insecure tools like Telnet and provides a simple, secure way to perform remote administration.
Overview
The diagram below illustrates how SSH establishes a secure, encrypted tunnel between a client and a remote network device. It highlights the authentication process, the encryption of management traffic, and the overall flow of communication used to ensure secure remote access.
SSH Basic Architecture
SSH uses a client–server architecture to provide secure remote access over an untrusted network. When an SSH client initiates a connection, the server presents its host key so the client can verify its identity and prevent man-in-the-middle attacks. After trust is established, both sides negotiate encryption algorithms and create a secure session key using a key-exchange method.
The user then authenticates—commonly with a password or public key. Once authenticated, all data sent between the client and server is encrypted, maintaining confidentiality and integrity. This architecture allows secure command-line access, file transfers, and tunneling, making SSH a fundamental tool for network administration.
SSH Security Layers
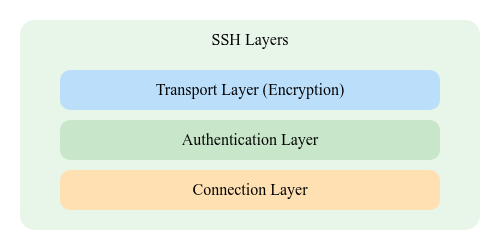
SSH uses three main security layers. Transport Layer establishes a secure, encrypted channel and protects against eavesdropping and tampering. User Authentication Layer verifies the identity of the client using passwords, keys, or other methods. Connection Layer manages multiple logical channels inside the encrypted tunnel, allowing secure remote commands, file transfers, and port forwarding.
SSH Inside a Device
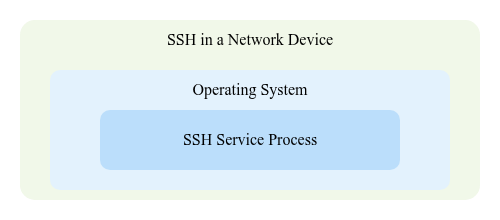
SSH provides secure remote management by encrypting all communication between an administrator and a network device. Inside the device, SSH runs as a server process that listens for incoming connections on TCP port 22. When a client connects, the device presents its host key, negotiates encryption, and requires user authentication—typically through a username and password or key pair. Once authenticated, the administrator gains secure CLI access, protecting configuration commands and sensitive data from interception.
SSH Key Authentication
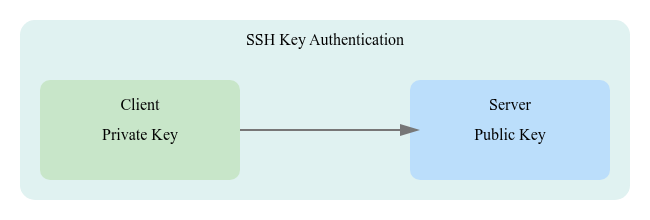
SSH key authentication uses a public–private key pair to securely log in without sending passwords over the network. The client stores the private key, while the public key is placed on the SSH server. During login, the server challenges the client to prove it holds the private key. If successful, access is granted without revealing any secret. This method improves security, prevents brute-force password attacks, and is commonly used for administrative access to network devices and servers.
SSH vs Telnet
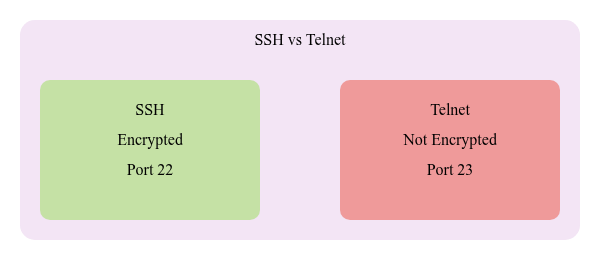
SSH and Telnet are both protocols used for remote device access, but they differ significantly in security. Telnet sends all data—including usernames and passwords—in plain text, making it vulnerable to packet sniffing and attacks. It offers no encryption and is generally considered outdated for modern networks.
SSH, on the other hand, provides secure remote access by encrypting all traffic between the client and the device. It uses strong authentication methods, protects credentials, and prevents eavesdropping or tampering. SSH is the recommended standard for managing routers, switches, and servers in any production environment, while Telnet is typically disabled for security reasons.
Flow of a Secure SSH Session
1. Connection Initiation
The client initiates the session by connecting to the server on TCP port 22.
2. Server Identification
The server presents its host key, allowing the client to verify the identity of the device before proceeding.
3. Encryption Negotiation
Client and server negotiate the encryption algorithms and security parameters that will protect the session.
4. User Authentication
The user is authenticated using either:
- Username and password
- Cryptographic key pair (stronger option)
5. Secure Tunnel Establishment
After successful authentication, SSH forms an encrypted tunnel that ensures confidentiality and integrity of management traffic.
6. Secure Remote Management
All commands and device responses are transmitted through the encrypted channel, protecting the session from interception or tampering.
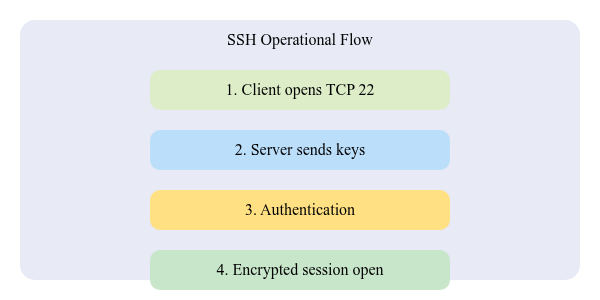
Operational Flow
Flow Diagram
Key Concepts
- Port 22 – Default TCP port used by SSH.
- SSH Protocol – Secure remote management using encryption.
- Public-Key Authentication – Uses a key pair instead of a password.
- Transport Layer Security – Provides encryption and integrity.
- SSH Daemon (sshd) – The server-side service listening for connections.
Steps
- Client Connects — TCP session to port 22
- Key Exchange — Encryption methods negotiated
- Authentication — Password or key
- Secure Channel — Commands and data encrypted
Authentication Mechanisms and Tunneling in SSH
Password Authentication
- User enters a password
- Simple but less secure
Key-Based Authentication
- Uses public/private keys
- More secure and recommended
SSH Tunneling
- SSH forwards traffic (like RDP or HTTP) through a secure tunnel
Components Table
| Component | Purpose | Explanation |
|---|---|---|
| SSH Client | Initiates the session | Laptop, PC, or terminal |
| SSH Server (sshd) | Listens on port 22 | Router, switch, Linux server |
| Keys | Secure identity | Public/private pair |
| Encryption | Protects data | Prevents snooping |
| Session Channel | Carries commands | Encrypted tunnel |
SSH Protocol Overview
- SSH
- Transport Layer
- Authentication Layer
- Connection Layer
- Supports keys and passwords
- Runs on TCP 22
Cisco CLI Section
conf t
ip domain-name lab.local
crypto key generate rsa modulus 2048
username admin privilege 15 secret MyPass123
line vty 0 4
transport input ssh
login local
exit
ip ssh version 2
end
write memory
Quick Guide
- SSH encrypts all management traffic
- Runs on TCP port 22
- Supports password and key authentication
- Always prefer SSH over Telnet
- Use RSA keys for stronger security
sshdis the server process on devices
CCNA Practice Quiz
- What TCP port does SSH use?
- What is the main improvement of SSH over Telnet?
- What command enables SSH on Cisco VTY lines?
- Which key type does SSH commonly use?
- What process listens for SSH connections on servers?
Answers
- TCP 22
- Encryption
transport input ssh- RSA keys
- sshd
Questions, comments, or just wanna drop a ‘hey’?
Email: fromzerotoccna@gmail.com
